It can take years to understand why and how certain individuals associated with terrorist organisations, such as ISIS leader Abu Bakr al-Baghdadi, are able to successfully influence large swaths of people and even longer to learn how to prevent them from doing so.
Our research suggests that in order to understand leadership – both within terrorist organisations, as well as across the organisations striving to ensure the safety and security of our populations – we need to rethink traditional assumptions about leadership and view leadership through a social network lens.
What is leadership?
Traditionally, organisational researchers have sought to understand leadership by focusing on the traits or behaviours of individual ‘leaders’. Leadership research has often progressed under the assumption that leaders possess some sort of formal authority over a set of subordinates, and that leaders and followers all share a single common group identity as in the case of the manager of a unit or the CEO of an organisation.
Leaders in terrorist organisations often break traditional moulds with regard to scholarly views of leadership. Terrorist leaders derive much of their power by operating outside of normal societal constraints and hierarchies, and they often use informal means to influence others both within, as well as outside, of their immediate groups.
Certainly, terrorist systems rarely conform to traditional models of organisations developed for the industrial revolution era. However, even in ‘traditional’ organisations, such as the military, governments and corporations, leadership does not always fit neatly into formal organisational hierarchy charts. People often influence one another informally, and these informal influence processes are not always exerted in support of organisational goals.
Our work, along with other leadership scholars, strives to better understand leadership in complex organisational systems by recasting leadership as an emergent social relationship that arises as at least one person attempts to influence another and at least one other person grants the influence attempt. The participants in leadership relationships may or may not occupy formal positions of authority and/or share a common group membership.
Clearly, in large and complex social systems, numerous people will participate in leader-follower processes in relation to one another, simultaneously or over time. Thus, leadership relationships form a complex web or ‘leadership network’ that emerges and evolves in response to changing situations.
Implications for security professionals
The view of leadership as a network yields at least three important implications for security professionals.
First, when considering how leadership shapes the success or failure of any operation, it is necessary to go beyond the impact of any individual leader to consider the impact of the network of leader-follower influence relationships. Research suggests there are certain leadership network patterns that are more or less beneficial for collective outcomes, over and above the effects of any individual leader.
For example, evidence shows that within small teams, a 'shared' pattern of leadership, where many members contribute to the leadership of the team, can have positive effects on team performance. Therefore, targeting a single leader, or a few leaders, in a terrorist cell may not sufficiently alter the direction of the collective.
Targeting a single leader, or a few leaders, in a terrorist cell may not sufficiently alter the direction of the collective
Second, in order to predict how and why influence will come about, we need to move beyond thinking only about the characteristics of potential leaders, such as their personality traits and experience. Like other types of social networks, leadership networks come about not only due to attributes of individual leaders but also due to characteristics of both followers and of the social contexts they operate within, including group norms and the patterns of other networked social connections (e.g. advice, friendship, communication). Predictions regarding who will lead and who will follow could be significantly enhanced by considering these multilevel drivers of leadership networks.
Finally, in order to remain adaptive and competitive in this challenging era for national security, we may need to rethink how we develop leadership within the organisations that ensure the safety and security of our populations.
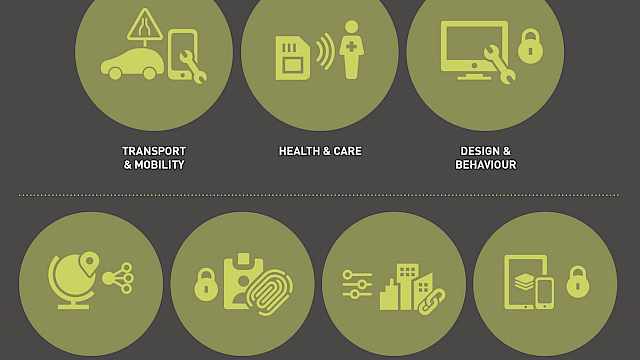
Our research surveying over 200 leadership development practitioners suggests that networks might be incorporated into leadership development in at least three ways.
- Based on research linking certain central positions in other social networks with leadership influence, formal leaders should be trained to understand and leverage their own social networks to enhance their influence.
- it is important to train individuals to understand the social and leadership relationships of others—both within as well as external to their own groups. By better understanding why, how, and among whom influence is likely to arise, formal leaders will be better able to leverage, and potentially alter, others’ networks to enhance security.
- Given the link between leadership network patterns and collective success, leadership development might take seriously the challenge of creating entire systems of effective patterns of informal leadership connections.
There is potential for leadership systems to be enhanced through organisational structures and work practices that foster social connectivity, as well as through team-training strategies targeting the leadership and teamwork skills of entire teams, or systems of teams.
Read more
- Carter, DeChurch, Braun, & Contractor (2015) Social network approaches to leadership: An integrative conceptual review. Journal of Applied Psychology, 100, 597–622;
- Cullen-Lester, K.L., Maupin, C.K., & Carter, D.R. (2017). Incorporating social networks into leadership development: A conceptual model and evaluation of research and practice. The Leadership Quarterly, 28, 130–152.
Copyright Information
As part of CREST’s commitment to open access research, this text is available under a Creative Commons BY-NC-SA 4.0 licence. Please refer to our Copyright page for full details.